Operate safely
Build securely

This analysis is based on publicly available on-chain data and post-exploit reports from Chainalysis, PeckShield, Cyvers, and independent researchers. Where contract source code is reconstructed from bytecode analysis or secondary sources, this is noted. Dedge Security provides digital assets Security Posture Management (SPM) assessments covering smart contract architecture, cloud infrastructure posture, compliance alignment, and operational incident response design.
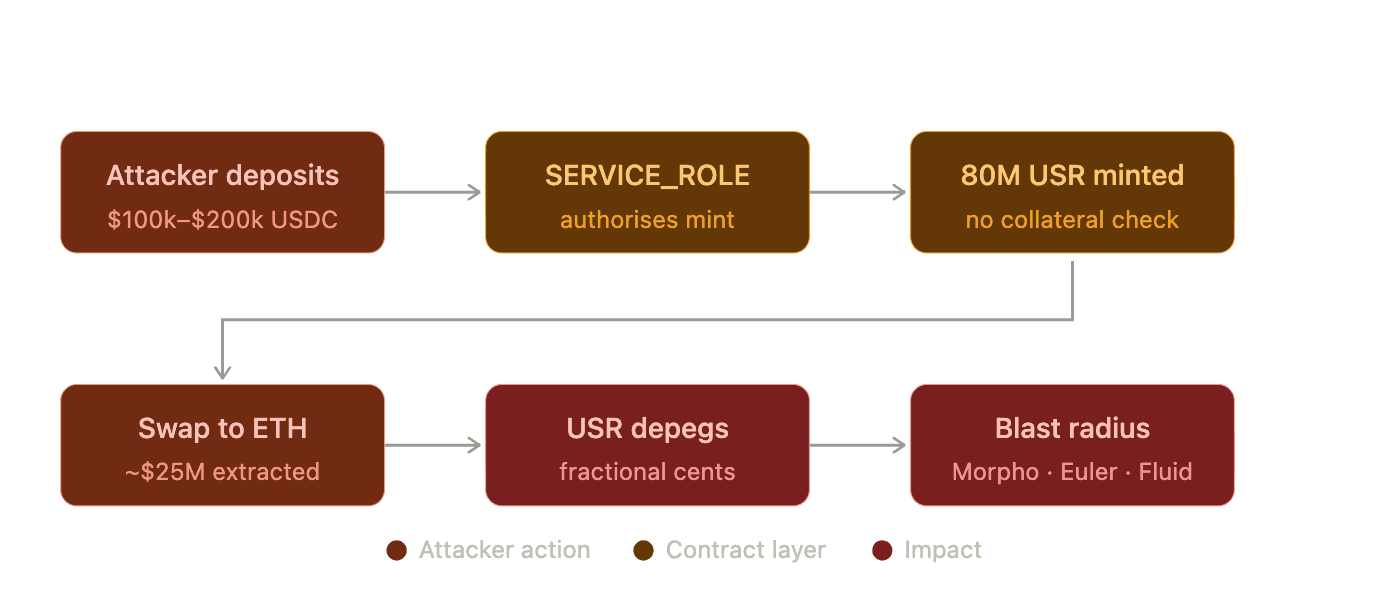
On 22 March 2026, an attacker deposited between $100,000 and $200,000 in USDC into Resolv's USR Counter contract and walked away with approximately $25 million in ETH. Two transactions, 50 million USR and 30 million USR, were minted in minutes using a compromised SERVICE_ROLE key. USR depegged within seconds. The blast radius extended to Morpho, Fluid, Euler, and Inverse Finance.
The smart contracts executed correctly. This was not a bug in the conventional sense. It was a case of overly trusting off-chain infrastructure combined with an absence of on-chain safeguards that would have contained the damage.
Eighteen audits. A $500,000 Immunefi bug bounty. Neither caught what we outlined below.
Finding 1: Missing maxSupply Check Relative to Deposited Collateral
Severity: Critical. Detectable at code review.
The USR Counter contract defines a minimum USR output amount but imposes no upper limit. There is no on-chain validation of the ratio between collateral deposited and USR minted. No price oracle integration. No total supply cap. No maximum mint ratio. Any quantity signed by the SERVICE_ROLE key is executable by the contract.
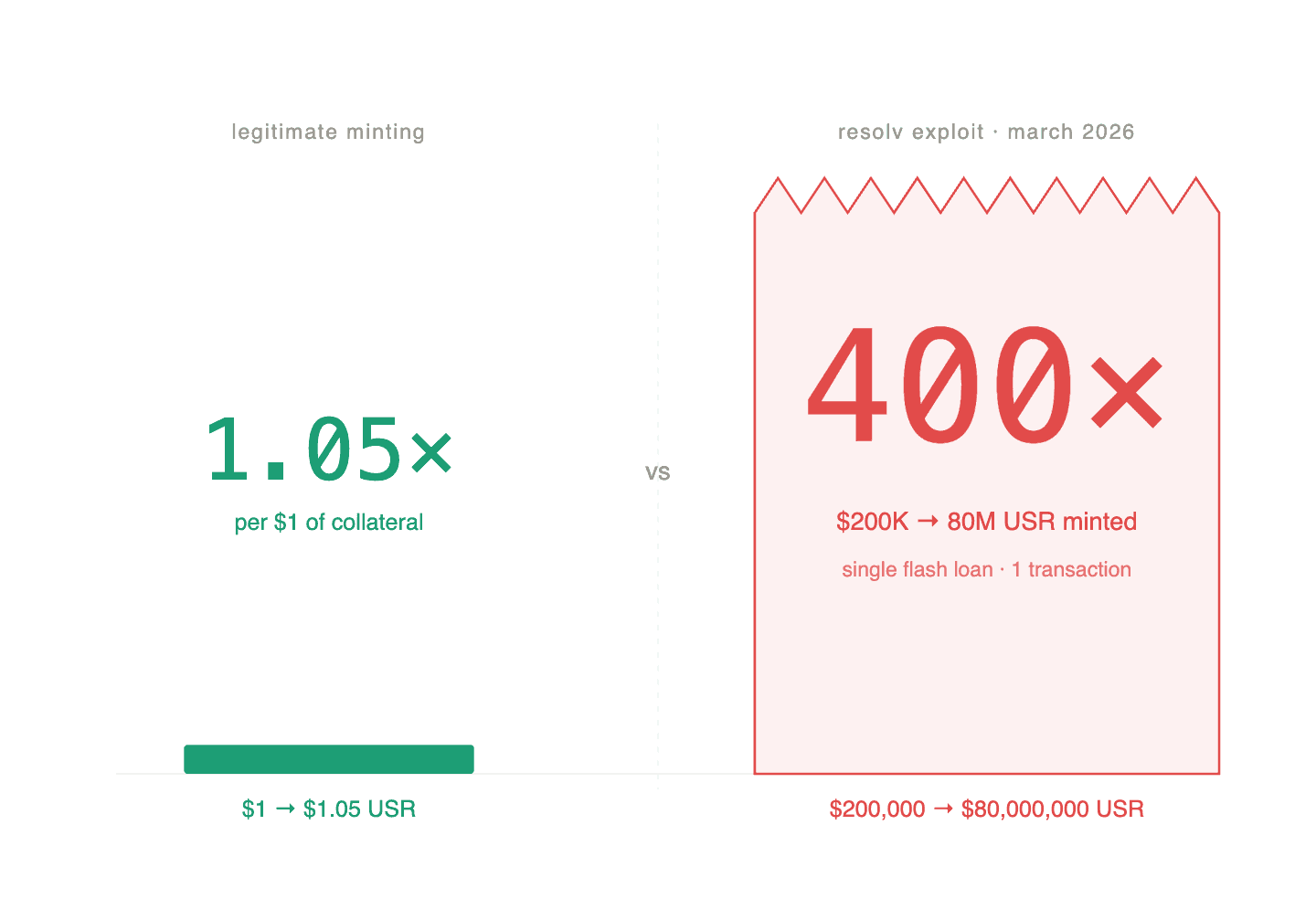
A supply ceiling enforced on-chain relative to USDC held in the contract vault would have made this exploit economically non-viable, regardless of whether the signing key was compromised. The attacker achieved a 400x leverage ratio: $200,000 in USDC producing 80 million USR. A collateral-ratio guard set at, say, 1.05x would have rejected both transactions outright.
What SPM flags: checks for the presence of maxSupply or collateral-bound minting caps in smart contracts where minting is controlled by an off-chain or privileged role. Where the backing collateral is accessible on-chain through a vault address or oracle feed, we flag the absence of this check as a critical finding. In the Resolv architecture, the USDC deposits to the USR Counter contract are on-chain and verifiable. The absence of a ratio check tied to that balance is detectable at the code level.
Note: Where collateral valuation depends entirely on off-chain oracles not referenced in the contract, this check requires additional context.
Finding 2: Overly Permissive Cloud Infrastructure and Single-Key Privileged Role
Severity: Critical. Partially detectable without source code.
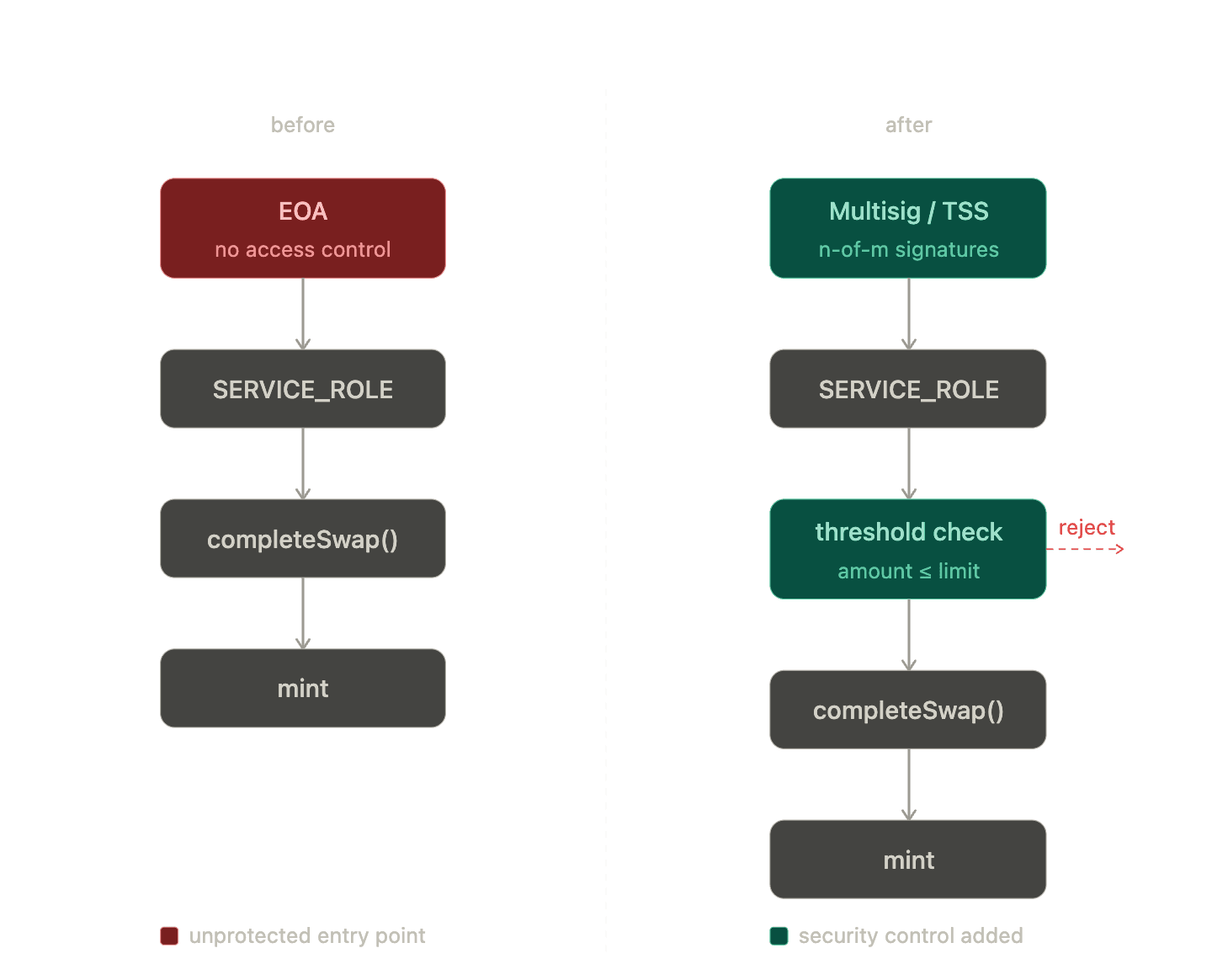
The SERVICE_ROLE, which holds sole authority to finalise minting amounts via completeSwap, was controlled by a single externally owned account rather than a multisig. The attacker gained access to this key through Resolv's AWS Key Management Service environment.
Two compounding failures are present here:
First, the architectural decision to vest minting authority in a single EOA rather than a multisig or threshold signing scheme.
Second, the storage of that key in a cloud KMS environment with insufficient access controls.
What SPM flags: Assesses cloud credential configuration as part of the infrastructure posture layer of a Web3-native SPM engagement. Overly permissive IAM policies, singleton key custody for privileged protocol roles, and the absence of hardware security module controls are flagged explicitly. We cannot confirm the precise misconfiguration in Resolv's AWS environment without access to their infrastructure configuration, but this class of finding is within scope for our infrastructure posture checks.
At the contract level, the use of a single EOA for SERVICE_ROLE rather than a multisig is a detectable architectural weakness. This is flagged in the compliance scan.
Finding 3: No Automated Pause Mechanism and a Four-Hour Incident Response Window
Severity: High. Enforceable at the compliance layer.
Resolv Labs paused all protocol functions after confirming the breach. The exploit began at approximately 02:21 UTC. The pause came hours later, after tens of millions in ETH had already been extracted and converted.
A $100,000 USDC deposit authorising 50 million USR is an anomaly that no legitimate user would ever generate. An alert on this function call pattern, with a threshold flagging ratios above 1.5x the normal range, would have identified both primary transactions instantly.
The protocol had a pause function. The issue was not capability. It was the absence of any automated or near-real-time trigger connected to that function.
It is also worth noting that the ability to freeze funds and pause contract activity is a compliance requirement under the Genius Act for stablecoin issuers. This is not a best practice recommendation. It is a regulatory obligation.
What SPM flags: The compliance scan checks for the presence and accessibility of freeze and pause mechanisms in the contract scope. Absence of a pause function, or presence of a pause function with no documented trigger criteria, is flagged as a compliance gap.
On the automation side: Dedge's monitoring layer can surface alerts when anomalous minting activity breaches defined thresholds. We do not currently automate contract pausing directly at the transaction level. We can, however, design the alerting architecture and document the trigger logic such that an operations team or a downstream automation layer can act on it with minimal latency. The four-hour window in this incident is not a monitoring problem. It is an incident response design problem.
Summary | ||
|---|---|---|
Finding | Layer | Detection Point |
No collateral-bound mint cap | Smart contract | Code review |
Single EOA SERVICE_ROLE, permissive KMS | Infrastructure | Infrastructure posture management |
No automated pause trigger | Compliance and operations | Compliance scan and incident response design |
Resolv underwent 18 audits. Point-in-time code review does not cover cloud infrastructure posture. It does not enforce compliance controls. It does not design incident response triggers. These are not audit findings. They are security posture findings, and they require a different kind of assessment.
If you are building or advising a stablecoin protocol, a tokenisation platform, or any system with a privileged off-chain minting role, and you have not reviewed your posture across all three of these layers, it’s time to have that conversation.
DM’s open!
Connect with us on: